Seperti judul postingan ini yang membahas tentang bisnis online gratis di internet menggunakan blog blogspot untuk pemula, maka di bawah ini saya mencoba membuat beberapa jawaban sesuai dengan pengalaman saya membuat blog dan mencoba me-monetize (menghasilkan uang) blog, khususnya untuk teman yang menggunakan blog gratisan. Agar lebih mudah dipahami buat teman-teman yang masih pemula , postingan ini bukanlah panduan secara detail tetapi mungkin semacam sekilas tinjauan tentang cara cari uang di internet dengan modal blog gratisan blogspot, maka saya buat menjadi semacam postingan tanya jawab (sumber pertanyaan dari email teman-teman yang pernah menanyakan tentang bisnis online ke email saya), seperti di bawah ini:
1. Apakah blog dengan sub domain blogspot (blogger) bisa ikutan bisnis online.
Bisa.
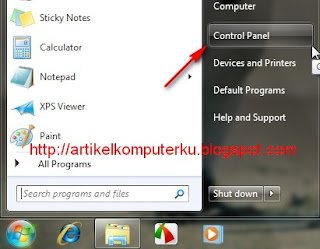
Jika anda membuat blog di blogspot maka anda akan mendapatkan sebuah blog sub domain blogspot yang bisa anda kelola, contoh blog saya: http://artikelkomputerku.blogspot.com, anda bisa menggunakan blog tersebut untuk mengikuti bisnis online tanpa khawatir di banned oleh blogger (google)
2. Bisnis online apa saja yang bisa diikuti:
Jawaban:
berikut ini adalah program bisnis online di internet yang gratis biaya pendaftaran yang saya rekomendasikan:
a.bisnis online PPC (Pay per click) Lokal
b.bisnis online Google adsense (Pay per click mancanegara)
c.bisnis online text link ads (jualan link)
d.bisnis online affiliasi amazon
3. Bagaimana cara kerja pcc dan apa saja ppc lokal yang terpercaya (realible)
Jawaban:
PPC Lokal (pay per click), adalah sebuah program periklanan yang mempertemukan antara advertiser (pengiklan) dan publisher (blogger) dimana anda akan dibayar setiap ada pengunjung yang klik iklan ppc yang ada di blog anda.ada juga ppc yang memberikan bayaran tertentu setiap iklan dibuka /tampil per 1000 kali.
Untuk mengikuti program ppc ini, anda harus mendaftar ke situs penyedia ppc, kemudian copy script ppc yang ada di member area, selanjutnya masukan script ppc ke blog anda, maka saat blog anda dibuka akan muncul iklan ppc-nya
saat ini ada beberapa ppc yang bisa anda ikuti:
kumpulblogger, kliksaya, adsensecamp, ppc indo, biindit, dll
Besarnya komisi bervariasi dari Rp.150 hingga Rp.350/klik untuk iklan reguler. Biaya pendaftaran gratis.
4. Apakah blog gratisan bisa ikutan Google adsense dan bagaimana cara kerja google adsense
Jawab:
Blog gratisan blogspot (blogger) bisa ikut google adsense.
Google adsense merupakan sebuah program periklanan berbasis ppc (milik google) yang bisa anda ikuti untuk menghasilkan uang dari blog anda, ada beberapa fitur /jenis program periklanan yang ditawarkan oleh google adsense:
Untuk account berbahasa indonesia (saat mendaftar anda menggunakan blog berbahasa Indonesia, dan memilih languange "Indonesia") hanya tersedia google adsense for search, google adsense for feed, google adsense for domain. Jika saat mendaftar google adsense anda menggunakan blog berbahasa Inggris dan memilih language "English", akan ada tambahan adsense text ads.
a. Google adsense for search , adalah sebuah fasilitas pencarian web yang di lengkapi dengan iklan dari google, penghasilan diperoleh dari pengunjung yang klik iklan, biasanya di bagian atas halaman pencarian akan muncul iklan di tandai dengan kotak Ads by Google(iklan tidak selamanya muncul, tergantung keyword yang diketik di kotak pencarian).
Contoh google adsense for search bisa dilihat disini
google adsense
b. Google adsense for feed
Google adsense for feed adalah program adsense google yang bisa anda gunakan untuk memasukkan iklam google ke dalam feed blog anda.
Contoh adsense for feed bisa dilihat disini:
Adsense feed indonesia
Adsense feed englih
c. Google adsense ads (text ads + image ads +video ads)
Iklan ini hanya ada jika account blog anda berbahasa inggris, bisa berjalan dengan baik di blog yang konten (isi postingannya) berbahasa Inggris, namun terkadang ada beberapa blogger yang memasang di blog berbahasa Indonesia. iklan text ads terkadang muncul terkadang hanya public ads (tergantung keyword).
penghasilan blog anda bersumber dari pengunjung yang kilk iklan google yang terpasang di blog anda. di bagian header ada iklan dari google.
Contoh blog saya yang terpasang iklan text ads google adsense bisa dilihat disini:
google adsense ads
d. Google adsense for domain
Biasanya jika blogger punya domain ( membeli/menyewa domain berbayar), jika menyewa beberapa domain dan belum sempat mengupdate /mengisi domain tersebut, maka terkadang menggunakan domain tersebut di parkir di situs yang menyediakan layanan domain parking. Biasanya domain yang mengikuti program periklanan domain parking, di situsnya hanya berisi link-link sponsor (iklan), jika ada pengunjung yang masuk ke situs tersebut maka bingung untuk keluar karean ayang ada hanya link iklan saja, bolak balik klik sana klik sini akan membuak situs iklan, penghasilan pemilik domain tersebut kana mendapatkan hasil dari klik pengunjung terhadap link sponsor.
5. Apakah blog berbahasa Indonesia bisa ikut google adsense
Jawab:
Blog berbahasa Indonesia (berbayar/gratisan (blogspot)) bisa ikut program google adsense.
6. Bagaimana cara ikut google adsense bagaimana tips untuk cepat di approve google adsense
Jawaban:
Untuk mempercepat blog diterima google adsense:
1. Anda harus punya blog (bisa menggunakan blogspot, blog berbayar biasanya lebih diprioritaskan),saya dulu mendaftar google adsense pakai blogspot dengan blog artikel komputer bulan desember 2008 (disetujui februari 2009) , selanjutnya mencoba peruntungan dengan membuat blog berbahasa Inggris (hasil dari terjemahan google translate) proposal dimasukkan bulan april 2009, alhamdulillah ternyata diterima bulan juni 2009, jadi sekarang semua blog pakai iklan dari akun dari google adsense english. Sampai saat ini belum punya blog domain berbayar,masih setia dengan blogspot.
2. buat postingan minimal 10 , gunakan konten (isi postingan yang original), umur blog minimal 6 bulan (dulu umur blog saya masih 2 bulan langsung daftar karena modal coba-coba dan belum ada aturan umur blog 6 bulan), sebaiknya selama mengajukan permohonan google adsense anda terus update blog anda, kurangi isi blog yang berisi link affiliasi atau link referal
3. Saat mendaftar google adsense, hindari mengikuti program ppc sejenis seperti adbrite,bidvistizer, dll
4. Gunakan template yang sedikit dimodifikasi, agar google mengira anda akan bakal serius ngeblog)
5. Daftarkan blog anda ke google webmaster tools, dan lakukan verify blog anda agar google mengira anda bakal menerapakan teknik seo dalam mengembangkan blog
6. Usahakan Page rank naik saat menunggu proses approve google adsense
7. Usahakan jumlah trafik (pengunjung) bertambah saat menunggu proses approve google adsense
8. Berdoa ...dan berdoa...kepada Allah SWT,mudah-mudahan menggerakkan hati tim google untuk menyetujui blog anda, karena yang menilai blog anda disetujui atau tidak adalah staf marketing google adsense.
7. Bisakah blog dengan domain blogspot ikut bisnis online text link ads (jualan link)
Jawaban:
Untuk teman pengguna blogspot, tidak perlu berkecil hati saat ini ada blog dengan domain blogspot sudah diperhitungkan oleh situs penyedia layanan text link ads.
Beberapa contoh situs penyedia layanan teks link ads yang menyedia publisher dari blog domain blogspot adalah : ask2link, textlinkads, blogrollplease, dll
Agar dapat mengikuti text link ads anda harus meningkatkan pagerank dan trafik blog anda.
8. Bisakah blog blog dengan domain blogspot ikut bisnis online Affiliasi Amazon
jawaban:
Bisa. Anda cukup mendaftarkan blog anda ke situs amazon, kemudian mengambil scipt link produk, widget,
toko online amazon (online shop amazon) dan saat ini di blogger (akun bahasa inggris) sudah ada fasilitas untuk mengintegrasikan link amzon dan tek editor blogspot, jadi saat anda membuat postingan anda bisa menambahkan link produk amazon yang berhubungan dengan tema postingan.
Sebenarnya masih banyak bisnis online yang bisa diikuti dengan hanya bermodalkan blog blogspot. Postingan di atas saya buat karena sudah mulai menghasilkan uang dollar walaupun masih sedikit).Untuk sementara sampai disini dulu postingan saya, lain kali di sambung dengan rincian yang lebih detail.
Keberhasilan bisnis online bergantung pada kesungguhan anda dalam berbisnis di internet, jangan mudah terpanting dengan postingan mendapatkan jutaan hingga miliaran dalam sebulan. Mulailah bisnis online dari yang kecil-kecil dulu mungkin buat pemula bisa menghasilkan uang ratusan ribu perbulan jika semakin berkembang bisa dapat jutaan perbulan.
Namun semuanya tergantung pada kesungguhan membuat blog,kontent berisi keyword yang high price keyword, dan dioptimasi dengan
teknik SEO agar ada pengunjung blog anda.
Referensi:
Bisnis Online